Key Points
- Understand CMMC: The Cybersecurity Maturity Model Certification (CMMC) is a DoD cybersecurity framework designed to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) across the Defense Industrial Base (DIB).
- CMMC 2.0 rollout: The final rule, 32 CFR Part 170, took effect in December 2024; the DFARS 252.204-7021 rule is expected in November 2025, with a four-phase rollout across new DoD solicitations.
- Three certification levels:
- Level 1 (Foundational): 15 safeguarding requirements from FAR 52.204-21; annual self-assessment and affirmation in SPRS.
- Level 2 (Advanced): 110 security controls from NIST SP 800-171; self-assessment for non-prioritized or C3PAO certification for prioritized programs; POA&Ms closed within 180 days.
- Level 3 (Expert): Based on NIST SP 800-172; DIBCAC-assessed every three years; focused on APT defense and proactive threat detection.
The Cybersecurity Maturity Model Certification (CMMC) establishes cybersecurity processes, practices, and requirements to safeguard sensitive and unclassified information shared by the Department of Defense (DoD) and its contractors and subcontractors. Specifically, it aims to protect the Defense Industrial Base (DIB) from more complex cyberattacks.
CMMC 2.0 was announced in November 2021. The final program rule (32 CFR Part 170) took effect in December 2024. Contractual enforcement will begin once the DFARS acquisition rule is finalized (under OIRA review as of July 2025). The DoD will phase in requirements into solicitations in four stages, starting from the effective date.
This article discusses how to get CMMC certified and everything you need to know to become CMMC compliant.
🥷 Keep yourself updated with the latest IT news with the NinjaOne weekly newsletter.
What is CMMC?
CMMC, which is not the same as the CCSK, stands for the Cybersecurity Maturity Model Certification. This is a new standard that applies to all contractors and subcontractors of the Department of Defense (DoD). The certification was designed as a cybersecurity framework to ensure the protection of sensitive unclassified information. It also acts as a guard against supply-chain-style attacks by cybercriminals.
The CMMC ensures that DoD suppliers and contractors protect sensitive information and maintain a strong cybersecurity posture. It builds on NIST SP 800-171 at Level 2 and adds selected requirements from NIST SP 800-172 at Level 3.
What is the CMMC 2.0 model?
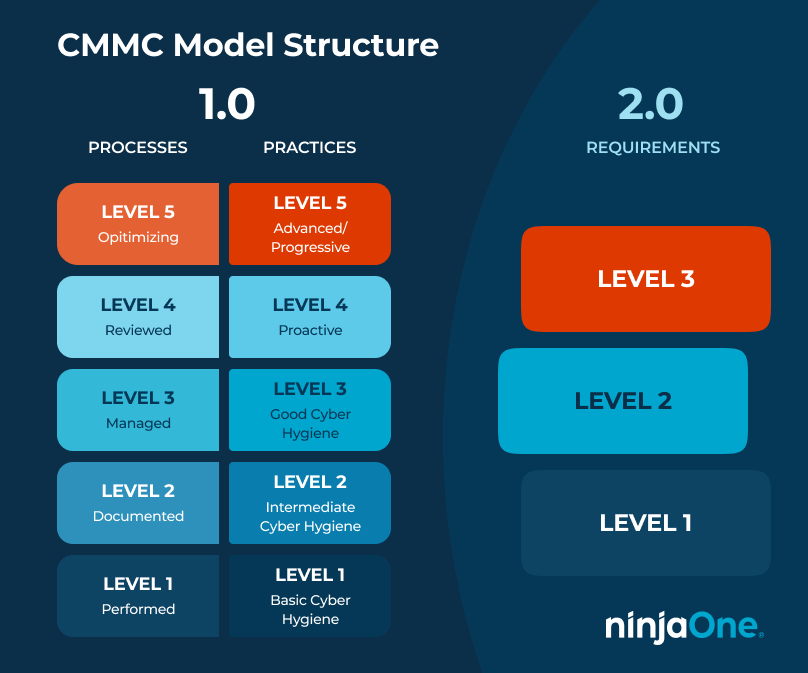
CMMC 2.0 is the next iteration of the initial cybersecurity model. The 1.0 model featured a five-level rating system, with each level progressively becoming more challenging and expensive. Meanwhile, the 2.0 program streamlines these requirements to three levels.
- Level 1 is required for organizations working with Federal Contract Information (FCI). This only requires basic cybersecurity strategies as defined in FAR 52.204-21, “Basic Safeguarding of Covered Contractor Information Systems.” It focuses on safeguarding Federal Contract Information (FCI). Additionally, CMMC level 1 requirements include security assessments and awareness training.
- Level 2 is required for organizations working with Controlled Unclassified Information (CUI) and complies with the 110 security controls defined in NIST 800-171, “Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations.” The assessment type depends on the contract. Some allow self-assessment (every 3 years, with annual affirmation), while prioritized programs require C3PAO certification. POA&Ms may be used in limited cases with a 180-day closeout.
- Level 3 is the highest compliance level, intended for organizations working with CUI and targeted by Advanced Persistent Threats (APT). It requires compliance with NIST 800-172, “Enhanced Security Requirements for Protecting Controlled Unclassified Information: A Supplement to NIST Special Publication 800-171.” And, includes proactive strategies to detect and remediate threats. Certification is performed by the DoD’s DIBCAC on a triennial cycle with annual affirmations. As such, Level 3 also includes sophisticated detection and mitigation abilities and has system hardening
Remember that CMMC levels build off one another. Thus, you need to complete Level 1 to reach Level 2, and so on.
The updated structure also greatly simplified the goals to be:
- Safeguarding sensitive and military information.
- Enforcing DIB cybersecurity standards to meet evolving threats.
- Ensure accountability with CMMC compliance.
- Building a culture of cybersecurity and cyber resilience.
- Maintaining high public trust through professional and ethical standards.
CMMC 1.0 vs. 2.0
Both programs are essentially the same in protecting controlled unclassified information. Meanwhile, the 2.0 program made several key changes, which can be described as:
| Assessments | CMMC 1.0 | CMMC 2.0 |
| 5 increasingly progressive levels from Basic to Advanced. | 3 increasingly progressive levels.
| |
| Levels 2 and 4 are transition stages between levels 1, 3, and 5. |
- More streamlined model. CMMC 2.0 has only three compliance levels, compared to the previous model’s five (5). Additionally, CMMC 2.0 is more closely aligned with NIST cybersecurity models.
- Improved reliable assessments. CMMC 2.0 allows all companies at Level 1 and a subset of businesses at Level 2 to demonstrate compliance through self-assessments, resulting in higher accountability.
- Flexible implementation. CMMC 2.0 allows companies to create their own Plans of Action and milestones (POA&Ms). These are done within specified circumstances. It also enables the Government to waive the inclusion of CMMC requirements, given special conditions.
Why did the DoD make the CMMC 2.0 program?
After the launch of CMMC 1.0, DoD representatives received feedback from relevant stakeholders. Most comments about the 1.0 model concerned its current cost, and how to increase trust in the CMMC assessment ecosystem. This also includes clarifying and aligning its requirements with other federal and commonly accepted standards.
Who needs CMMC certification?
Any organization handling FCI or CUI must achieve CMMC certification at the level specified in its contract. If it does not have a contract yet, it is recommended that you apply for the level that best suits its current capabilities.
Take note that if you have a DFARS 7012 clause, you are subject to CMMC requirements.
❗If your contract includes DFARS 252.204-7012 and you handle CUI, expect Level 2 once CMMC is written into DFARS clauses. Current DFARS 252.204-7019/7020 already require NIST 800-171 self-assessment scores in SPRS.
What does CMMC mean for MSPs?
CMMC compliance for managed service providers (MSPs) working with DoD-connected clients may become a requirement. As such, should develop a plan for meeting CMMC Level 1 requirements. Doing so will allow the client’s business to continue running smoothly. This will also improve the overall security of non-DoD-connected clients. Many of the requirements of CMMC Level 1,, can be valuable services to include in your Managed Services Agreement (MSA). This includes the ability to provide security assessments and awareness training
For MSPs engaged with other parts of the federal and local government, some level of CMMC compliance may also become the new standard for public agencies. There is an increasing rate of company breaches and the demand for cybersecurity services. As a result, CMMC can serve as a useful guide to identify a pathway for growing the business.
When will CMMC become mandatory in contracts?
The Cybersecurity Maturity Model Certification Requirements (otherwise known as DFARS 252.204-7021) were published in January 2024. Its implementation and inclusion in contracts were described by March 2025. The acquisition rule (DFARS) is still pending finalization. This was submitted to OIRA in July 2025. DoD will introduce CMMC requirements in phases once the DFARS rule is effective.
That said, experts highly encourage organizations, contractors, and relevant MSPs to start their CMMC requirements as soon as possible.
Do I still need to comply with CMMC 1.0 now that CMMC 2.0 has been published?
Once CMMC 2.0 is codified in DFARS, the DoD will require all companies to adhere to the revised CMMC framework.
Currently, CMMC 1.0 is only required in select pilot contracts, as approved by the Office of the Under Secretary for Acquisition and Sustainment (OUSD (A&S))
How do I know what certification level I need?
Most contracts will require only Level 1 certification. This is an important first step all DoD contractors and subcontractors should take. Beyond that, new contracts will indicate the CMMC Level required.
How much does CMMC certification cost?
It is estimated that meeting CMMC Level 1, the lowest standard, will cost $3,000 to maintain every year.
From there, the CMMC certification cost for each subsequent level substantially increases. On average, the Department of Defense states that the cost of CMMC Level 2 is $100,000, at minimum. This number can increase. It will also depend on other factors, such as self-assessment and whether outside expertise will be needed.
What are the CMMC level requirements?
CMMC 2.0 requirements are heavily influenced by NIST standards and guidelines. We can summarize these requirements as follows:
| Level | Requirements | Assessment | Description |
| 1 | Meets 15 requirements in SP 800-171 | Annual self-assessment | Create and maintain:
|
| 2 | Meets Level 1 requirements and 110 standards determined by a third-party assessment. | Third-party assessment every three years. | Monitor and control:
|
| 3 | Must exceed 110 SP 800-171 requirements and Level 1 and 2 compliance. | Triennial assessments conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) | Implement and maintain:
|
How do I get CMMC certified?
- Conduct a self-assessment using NIST 800-171 standards.
- Create a plan of action and milestones (POA & Ms) based on your score from the self-assessment. Attempt to achieve the maximum score of 110.
- Submit the score to the DoD’s Supplier Performance Risk System (SPRS).
- Identify the scope of your services. Take note that Cyber-AB, the official accreditation body of the CMMC ecosystem, has only released the assessment guide for CMMC 2.0, Levels 1 and 2.
- Schedule a preliminary gap assessment by a third-party organization to identify gaps in your information security process. This step is optional, but recommended.
- Fix any identified security gaps found in step 5.
- Use the Cyber-AB marketplace to find a C3PAO like NSF-ISR to schedule your CMMC assessment.
- Undergo the CMMC assessment.
- Phase 1 includes the pre-assessment planning, identifying assessment team members, and developing a rough order of magnitude.
- Phase 2 covers the actual C3PAI assessment. It includes an analysis and review of objective evidence related to CMMC practices.
- Phase 3 is the post-assessment reporting, including a quality assurance review and any recommendations.
- Phase 4 may require remediation if your organization does not meet certain CMMC requirements. Typically, there is a 90-day timeframe to address any shortcomings.
- Receive your CMMC certification.
Remember that companies cannot submit their self-assessment for CMMC at the highest levels. Instead, third-party agencies conduct an unbiased audit and identify your organization’s security maturity level.
A managed services provider or third-party assessment organizers (C3PAOs) can help you better understand the CMMC framework. It will also tell you what improvements can be made to make the certification process easier.
Prepare your organization for CCMC certification by strengthening your security posture.
How NinjaOne helps IT pros get ahead of CMMC
Ensuring your services can be delivered through the cloud to accelerate CMMC compliance efforts and reduce costs. By leveraging cloud tools, IT pros can provide many CMMC practices. Specifically those that improve cybersecurity for the whole organization and mitigate risks.
Cloud-based remote monitoring and management software, such as the one offered by NinjaOne, can serve as important pieces in the cybersecurity toolchain. They accelerate the detection of vulnerabilities and management of security. But the tools can also be leveraged to coordinate and organize many core security functions, such patch management and antivirus.