The cybersecurity industry is a crowded and competitive market, with vendors pressured to differentiate themselves and keep up with competitors. These days, there’s a tendency for vendors to claim multilayered or “all-in-one” protection, but what that consists of varies. Not to mention how overwhelming the process of comparing offerings can be.
An acronym we’ve been seeing thrown around a lot lately is EDR, short for endpoint detection and response. Nearly every cybersecurity vendor is now saying they offer some form of EDR, so let’s define what it is and explain what it means for your cybersecurity stack.
📕 MSP’s Hype-Free Guide to EDR
What is EDR?
Endpoint detection and response (EDR) refers to endpoint security software designed to help organizations identify, stop, and react to threats that have bypassed other defenses.
Like other endpoint security software, EDR is deployed by installing agents on endpoints and is managed via a cloud-based SaaS portal. EDR plays a crucial role in enforcing cybersecurity within an infrastructure managed by an IT team or MSPs, providing a critical layer of defense against evolving cyber threats.
Note: This blog post touches on EDR at a high level, but if you’re interested in getting more details and learning how to evaluate EDR products, see our new MSP’s Hype-Free Guide to EDR. This comprehensive guide you can download for FREE distills extensive research into actionable insights.
How endpoint detection and response (EDR) work?
Endpoint detection and response are solutions with multiple tools/functions that work together. The list below shows how each function within an endpoint detection and response (EDR) solution works.
1. Collects and records telemetry data from endpoints
As CrowdStrike explains, EDR “records and stores endpoint-system-level behaviors.” An endpoint detection and response solution collects and records telemetry data and some contextual data from endpoint devices. Any activity on a device is collected and stored, such as programs that were started and files accessed, so the EDR solution can analyze behaviors and report anything out of the ordinary.
2. Monitors and analyzes endpoint activity
An endpoint detection and response system analyzes endpoint activity and user behavior using the data it collects. This is one of the main differentiators between other security solutions and EDR. Other solutions, such as antivirus, analyze files; EDR monitors and analyzes behaviors that occur on endpoints.
3. Alerts security experts of threats
When an EDR tool finds suspicious activity on an endpoint, it automatically alerts the cybersecurity team. Meanwhile, it also blocks malicious activity, and offers possible solutions to resolve the issue. Having an automated tool such as EDR that reduces IT teams’ workloads helps them focus on other critical tasks.
4. Resolve threats or breaches automatically
When an endpoint detection and response system finds a threat or breach, it instantly goes into action and attempts to resolve or minimize the damage. This feature helps IT security teams reduce the damage caused by cyber-attacks and resolve them as quickly as possible.
What are the benefits of EDR?
Now, let’s explore the key benefits that make an effective endpoint detection and response to cybersecurity:
-
Improved cybersecurity and protection
EDR solutions provide capabilities beyond the average antivirus solution when it comes to enhancing cybersecurity. Antivirus solutions may be efficient, but their signature-based threat detection might fail, especially in identifying threats that don’t match anything from the AV’s signature database. This is where EDR comes in. Besides identifying and stopping potential threats, EDR can actively scan and hunt for risks that AVs might miss, adding additional layers of support along with what cybersecurity systems can provide.
-
Deeper visibility
Endpoint detection and response allows for IT teams and MSPs to have a broader overview of their managed environment. The increased visibility that EDR software provides gives companies more knowledge about what’s happening in their network. This also gives them more confidence when responding to threats that attempt to infiltrate.
-
Rapid response
Rather than depending on manual efforts to react to threats, EDR can conduct automated response workflows. This prevents cyber threats from compromising your IT environment and can even restore resources to their original state in case they were compromised.
-
Proactive security
An endpoint detection and response tool can help maintain compliance with managed endpoints. It allows organizations to meet industry compliance requirements such as GDPR, HIPAA, PCI DSS, etc. By providing visibility into endpoint activities and the ability to detect and respond to threats promptly, EDR solutions help organizations demonstrate compliance with these regulations.
-
Improvement of data privacy
EDR and cybersecurity go hand in hand when it comes to employing actions that aim to protect an organization’s data. Data privacy has been an integral aspect of what cybersecurity and endpoint detection response tools try to prioritize. Utilizing EDR solutions helps guarantee data privacy by preventing unauthorized access to an organization’s sensitive information.
-
Cost saving
Lastly, employing an endpoint detection and response tool helps save companies from destructive data loss caused by cyber-attacks. EDR tools can help reduce the overall cost of a security breach by enabling faster incident response, minimizing downtime, and preventing data loss.
How do EDR tools empower organizations?
At a high level, EDR solutions gather data from endpoints, use that data to identify potential cybersecurity threats and provide helpful ways of investigating and reacting to those potential risks.
Historically, these capabilities were largely confined to big enterprise companies that could afford to have teams of experienced security analysts operating outside a security operations center (SOC). Sorting through troves of data, identifying suspicious activity, and understanding how to quickly react to incidents took considerable time, effort, and expertise.
In an effort to make these capabilities more accessible, cybersecurity vendors have worked on introducing EDR offerings that are less complex and centered more around streamlined workflows and automation. These “EDR Lite” solutions aim to lower the entry and bring EDR capabilities to a segment of the market that sorely needs them: SMBs.
Now that we’ve discussed what EDR tools are and why they’re crucial for modern security, let’s dive deeper into the essential features that make an effective endpoint detection and response solution.
5 key features of an endpoint detection and response solution
Because there are many providers in the EDR market, finding an endpoint detection and response solution for your IT team can be difficult. To find the best solution for your organization, look for these five key features in endpoint detection and response tools.
1. Integration
An EDR that can integrate with your current system benefits your IT team. Always ensure that your EDR solution integrates smoothly with your other applications and tools. IT teams and MSPs should also consider utilizing a complete endpoint management tool that integrates with an efficient EDR solution for a holistic approach to endpoint protection.
2. Detection and remediation
One of the main components of an endpoint detection and response tool is finding and detecting threats. Additionally, an efficient EDR system should be able to remediate threats quickly and notify a security team ASAP. Choose an EDR solution with very strong threat detection and remediation abilities.
3. Usability
Spending hours figuring out how a new software solution works isn’t a productive use of time. To avoid this, select an EDR solution that is intuitive and easy for your team to use. Some solutions offer a centralized management console on a single pane of glass, which helps users gain even more visibility into their network security.
4. Scalability
As your organization and IT team grow, you’ll need a solution that grows with you and smoothly adapts to changes. Take a look at the scalability options of EDR solutions before making any final decisions.
5. Security
Since endpoint detection and response solutions collect and analyze data, you’ll want to check their security measures. This is to help ensure that your data remains safe and is handled responsibly.
NinjaOne endpoint detection and response integrations
NinjaOne provides remote monitoring and management (RMM) software that helps IT teams and MSPs manage their endpoints. Some popular endpoint detection and response tools that integrate with NinjaOne include:
-
Bitdefender
Bitdefender offers a cloud-based endpoint detection and response solution that uses real-time monitoring, data collection, threat detection, analysis tools, and automated response actions to provide organizations with advanced endpoint security and protection.
-
Malwarebytes
Malwarebytes endpoint detection and response is an effective EDR tool that offers attack isolation, auto-remediation, threat detection, ransomware rollback, and protection against advanced zero-day threats.
-
SentinelOne
SentinelOne provides an endpoint detection and response tool known for its ability to proactively hunt and detect threats, report endpoint telemetry data, remediate attacks, analyze data, and customize to a specific IT environment.
-
Crowdstrike
CrowdStrike is a leading cloud-based endpoint protection company that NinjaOne integrates with for endpoint detection and response. The platform is known for its rapid response and prevention capabilities. The company also offers additional security solutions such as threat intelligence, incident response, and IT hygiene to provide a comprehensive approach to cybersecurity.
Where does EDR fit in a modern cybersecurity stack?
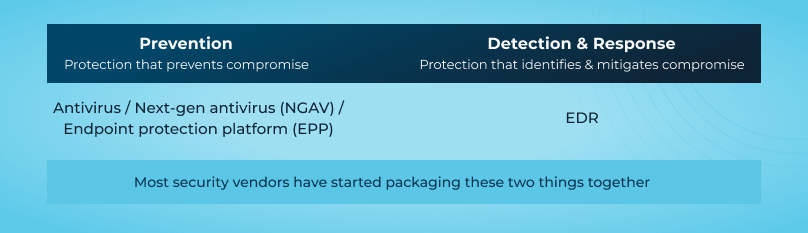
As a capability, EDR sits downstream from prevention-focused security solutions. Its primary purpose is to enable detection and response to threats once they have bypassed other defenses like firewalls and antivirus (AV).
That said, EDR functionality is rarely sold on its own anymore. Instead, it’s often packaged together with prevention-focused technologies like new generation antivirus (NGAV) to provide more unified endpoint security. So while “EDR” refers to a clearly defined set of capabilities, the lines separating EDR tools and other endpoint security tools have gotten incredibly blurry.
As Gartner puts it in its Competitive Landscape: Endpoint Protection Platforms, Worldwide, 2019 report:
“On the marketing front, many of the providers in the [endpoint security] market now look drastically similar to each other, touting machine learning and behavior-based analysis concepts — making it harder for organizations to make informed product decisions. Gartner believes that this is causing some confusion in the market.”
📕 MSP’s Hype-Free Guide to EDR
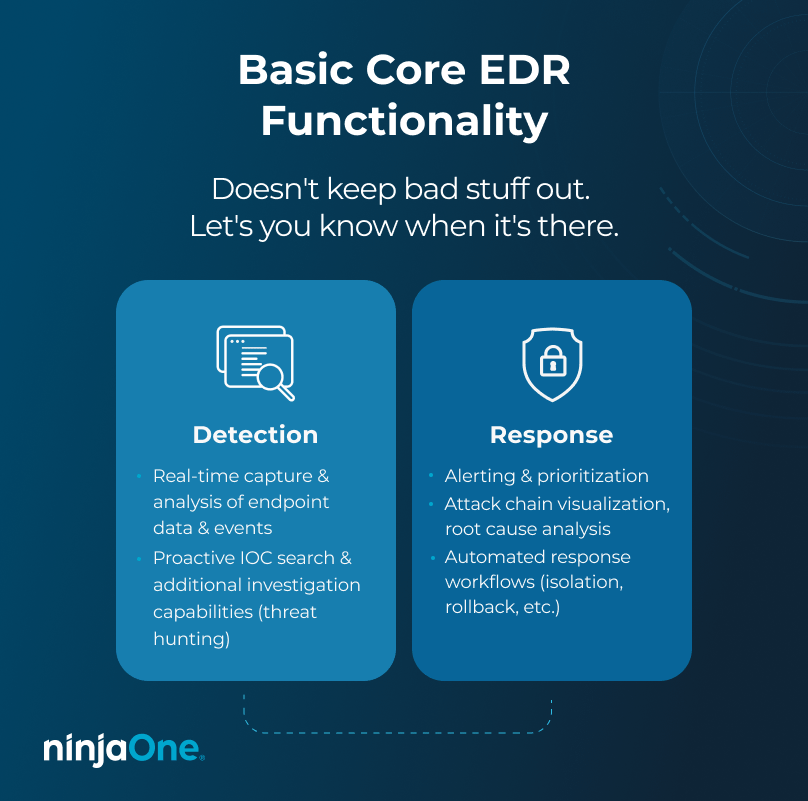
Specifically, the converging of AV/NGAV products with EDR products into single offerings has led to the (understandably) confused take that EDR tools are better AVs. That’s not right. While many EDR tools provide NGAV capabilities now, EDR functionality isn’t designed to keep bad things out. It’s designed to alert you when something potentially bad has broken in, and then help you react.
The truth is most vendors aren’t financially motivated to set the record straight on EDR. If potential customers are interested in it because they think it will block more attacks, they’re not going to correct them. But that makes researching and evaluating EDR solutions tricky, so to help we’ve put together a new guide that breaks everything down in clear, straightforward terms.
In the context of modern cybersecurity, endpoint detection and response tools are integrated with remote monitoring and management (RMM) tools and mobile device management (MDM) solutions. This integration empowers IT teams and MSPs by enhancing threat visibility and response across diverse environments.
By integrating EDR with both RMM and MDM platforms, organizations and IT teams can streamline their cybersecurity and endpoint management operations, allowing for quicker detection of threats across all types of endpoints, whether desktop, server, or mobile. This combination provides a more comprehensive defense, uniting prevention, detection, and management into a cohesive cybersecurity strategy.
Want more facts about EDR and tips for evaluating solutions?
Download your free 26-page MSP’s Hype-Free Guide to EDR. It addresses all your EDR questions, ensuring you’re prepared for inquiries from customers, bosses, or prospects.