NinjaOne now gives technicians the ability to directly manage their macOS devices via MDM. In addition to all the functionality provided by the NinjaOne RMM agent for macOS, Apple’s MDM protocol allows for additional capabilities that simply cannot be done using only an agent on the device. Technicians can now ensure NinjaOne is able to fully manage their Macs in the way that makes the most sense for them, whether that’s an RMM-only approach, or it involves bringing MDM into the picture.
The best part? RMM vs. MDM is not an either-or choice. These two solutions complement each other in NinjaOne, providing technicians an expansive feature set that covers all their macOS management needs. This starts at the very beginning of the device lifecycle. When taking a new Mac out of the box for the first time, using NinjaOne MDM you can automatically enroll it during the onboarding process, and the RMM agent will deploy to the device over the air, with no end-user interaction needed.
What does MDM mean for macOS management?
The MDM acronym itself stands for Mobile Device Management. On its own, this delightfully ambiguous term does not provide a lot of detail for the types of capabilities it brings to Apple device management in general, nor how these capabilities are distinct from an RMM-only offering. On Apple devices, the “MDM protocol” typically refers to a specific set of actions and configuration capabilities supported by the device OS that are initiated directly from a trusted MDM server and applied to the device. In an RMM-only approach, an agent application is installed on the device which then communicates with a remote management server. It is this agent that will ultimately perform actions and apply configurations on the device.
To many this might seem like a distinction with minimal difference. However, on macOS, and Apple devices in general, there are many capabilities that can only be used if initiated directly by that trusted MDM server. No matter how advanced or complex a device agent may be, certain capabilities may be significantly more difficult or even impossible in cases where that device is not managed directly by MDM.
Some examples of these types of capabilities include:
- Management of the device through its entire lifecycle, from the moment it is turned on and activated, and even staying managed through full device wipes
- Automatic approval and configuration of Privacy Preferences and System Extensions needed by many enterprise applications
- Easily approving, managing, and enforcing macOS updates
- Easily configuring and restricting core device functionality (such as Camera access or iCloud support), passcode requirements, network connectivity, and more
- Remotely and securely Lock or Wipe devices with the push of a button
How do I enroll a Mac into MDM?
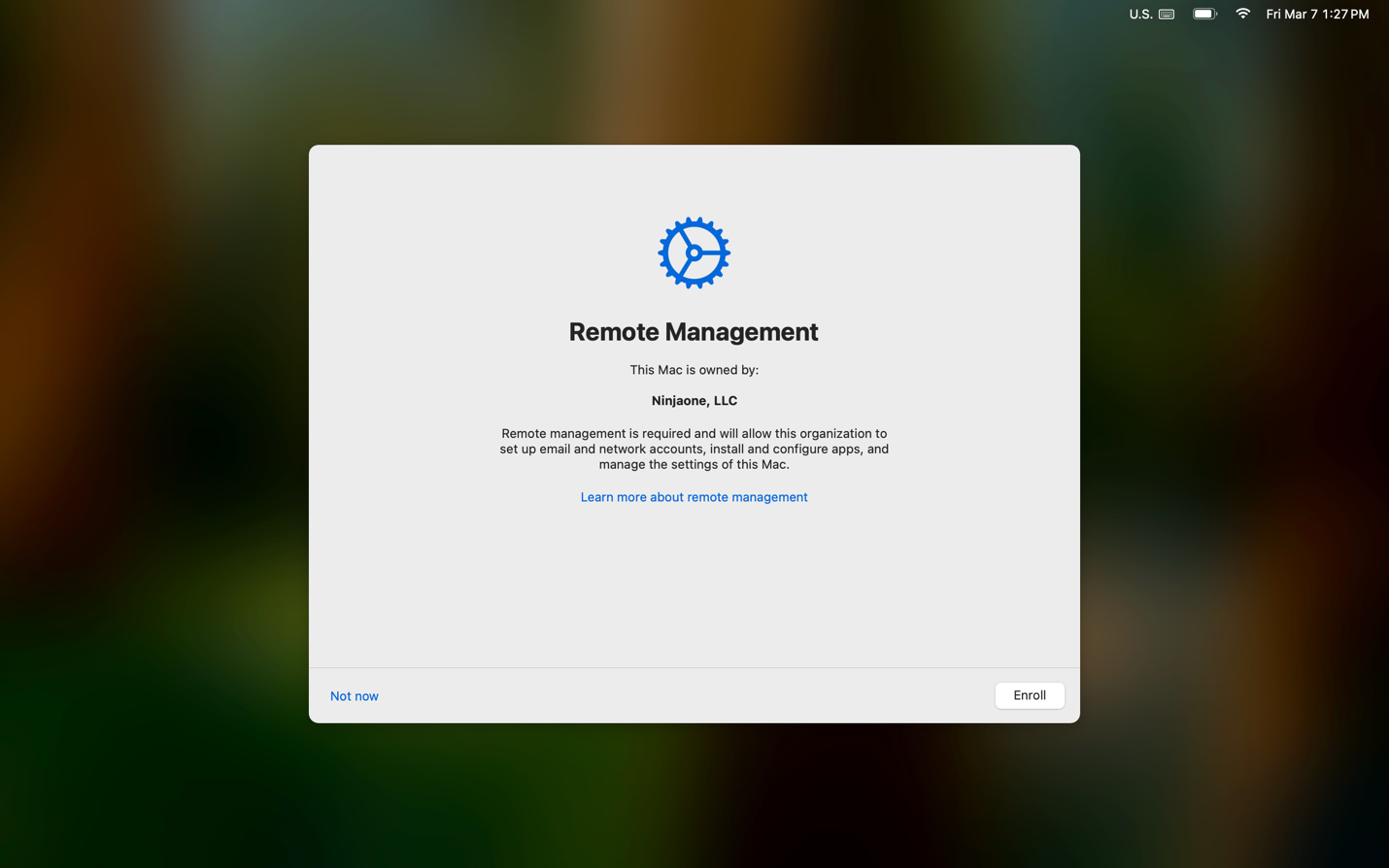
Technicians using company-owned Macs should set up an integration between NinjaOne and Apple’s Automated Device Enrollment. When enabled, any Mac will automatically enroll into NinjaOne MDM when the device goes through the initial Setup Assistant. This occurs when turning on a new device for the first time, or after a device wipe, such as when selecting the “Erase all Contents and Settings” option in the macOS System Settings.
Alternately, existing devices in the field can enroll into MDM without a device wipe. After setting up the ADE integration, and after removing any existing MDM profiles from the device, the following command can be used in Terminal to initiate enrollment. Note that this does require local administrator credentials on the device.
sudo profiles renew –type enrollment
Employee-owned devices, as well as devices that are not part of Apple Business Manager or Apple School Manager and cannot otherwise be added to those systems, can enroll by manually installing an enrollment profile. In NinjaOne, navigate to Add Item > Device > Computer > Mac. Set the distribution type to “MDM enrollment profile” and click “Generate installer.” You can download this file locally, copy a link, or directly email it to users. Simply download and install this file on a Mac, and the system will walk you through the MDM enrollment process.
What capabilities do I have after enrolling a Mac in MDM?
In addition to all supported macOS management capabilities offered by NinjaOne today, enrolling devices in MDM unlocks the following:
- Automatic deployment of the NinjaOne RMM agent
- Addition of MDM-based settings within the macOS Agent Policy
- Managing macOS updates
- Additional macOS device actions
Automatic deployment of the NinjaOne RMM agent
Immediately following MDM enrollment, the NinjaOne RMM agent will be automatically deployed to devices. The device will automatically allow most permissions required by the agent as well as NinjaOne Remote. While the ScreenCapture permission cannot be explicitly allowed, the device will be configured such that any local user account can allow it.
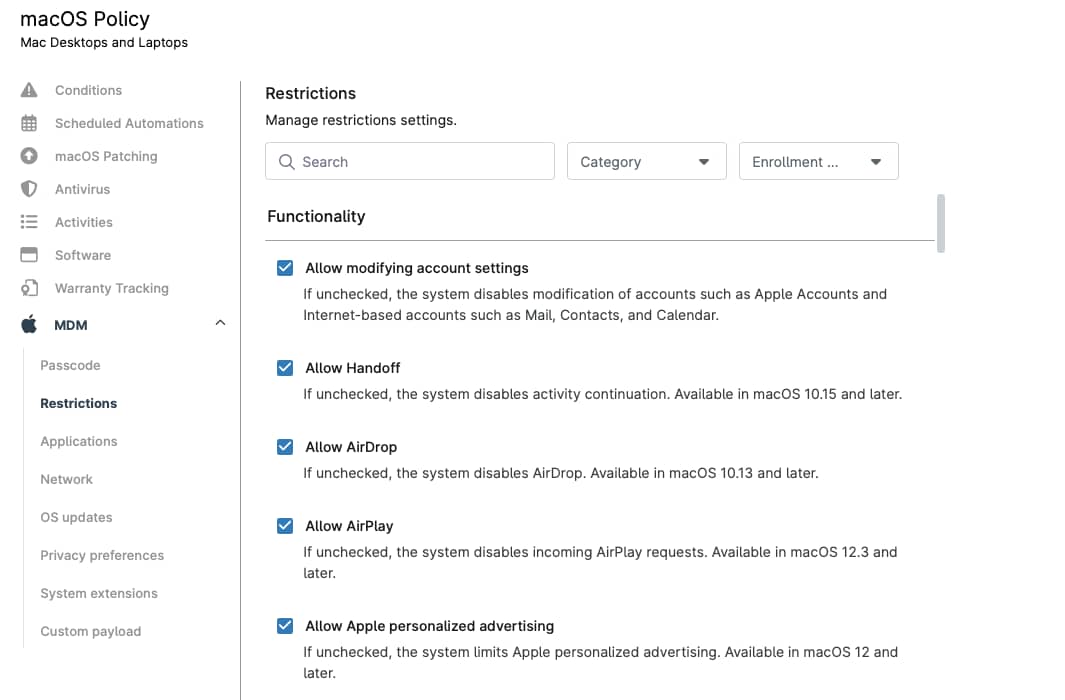
Addition of MDM-based settings within the macOS Agent Policy
Today in NinjaOne, policies for macOS devices are configured under Administration > Policies > Agent Policies. That will continue to be the case for MDM-enrolled devices. However, many new options will now be available.
The following payloads can be configured in the policy for MDM-enrolled devices:
- Passcode – Define minimum security requirements for the passcode of local user accounts on the device.
- Restrictions – Enable or disable many native device features, such as Handoff, AirDrop, iCloud, and various Apple Intelligence capabilities.
- Applications – Manage and deploy App Store-based macOS apps. By integrating with ABM and syncing a content token into NinjaOne, these apps can be automatically installed on managed devices. Apps that are deployed via a DMG or PKG installer can continue to be managed through NinjaOne as they are today.
- Network – Configure Wi-Fi networks or global proxies that devices are to connect to.
- OS updates – Define the default device behavior for how OS updates are handled. Additionally, manually approve and enforce specific macOS updates on devices.
- Privacy preferences – Automatically enable the various permissions, such as full disk access or accessibility access, that your third-party apps may require.
- System extensions – Automatically allow any system extensions that are needed for your enterprise applications to properly run on macOS.
In addition, technicians can define their own custom payloads to include in the policy. Custom payloads can be any mobileconfig file that are supported natively by macOS. This can include native macOS capabilities such as defining web content filters or app notification settings, or can define any managed preferences supported by any third-party macOS application.
Managing macOS updates
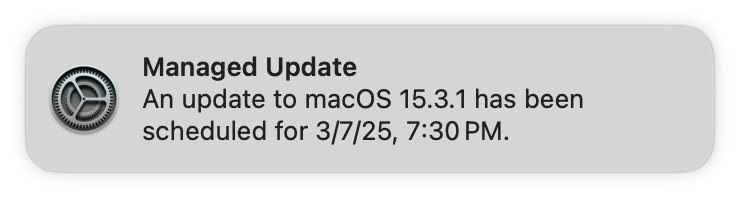
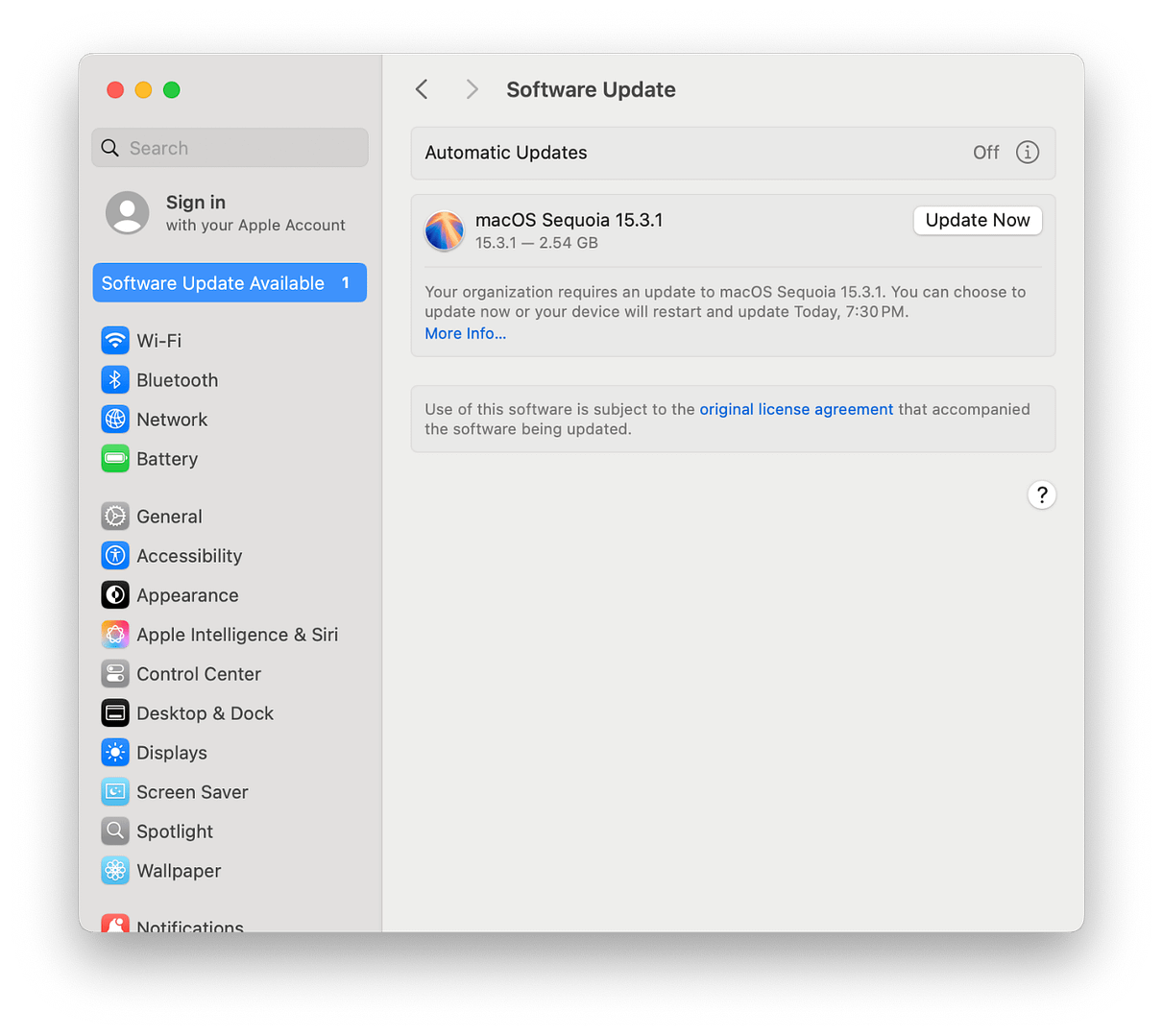
NinjaOne allows the easy management of macOS updates for all MDM-enrolled devices. Leveraging a subset of Apple’s MDM protocol known as Declarative Device Management (DDM), technicians are able to approve individual macOS updates and fully enforce them on devices by specifying an enforcement date and time. A typical approved update will behave with the following flow:
- Before approving an update, the technician will define standard device behavior in the OS Updates section of a policy. Typically, this will involve delaying when a particular update is available to end users. NinjaOne can delay an update from appearing to users of a device for up to 90 days from its release.
- A technician can approve a particular update, for example macOS 15.3.1. In doing so, they define an enforcement date and time. In this example, let’s say the enforcement date and time is set for the following Wednesday at 7:30pm.
- Upon approval, devices will receive a notification that macOS 15.3.1 has been approved for their device and will be enforced at the specified date and time. The update will automatically download and prepare on devices. Each day, they will receive a reminder that this update will be enforced at the specified time. Notifications become more frequent during the final 24 hours before the enforcement deadline. Users will be able to install the approved update at a moment of their choosing via these notifications, as well as through the normal device System Settings.
- If the enforcement deadline passes before the device has updated, then the device will force the update to occur. If the user is actively using a device, they’ll receive a 60-second countdown before the install occurs. If the device is not actively in use, the update will occur without any user interaction required.
In NinjaOne, an OS update can be approved from within the policy itself, as well as from the Patching > OS Patches dashboard. From the Patching Dashboard, updates can be approved across multiple policies at once.
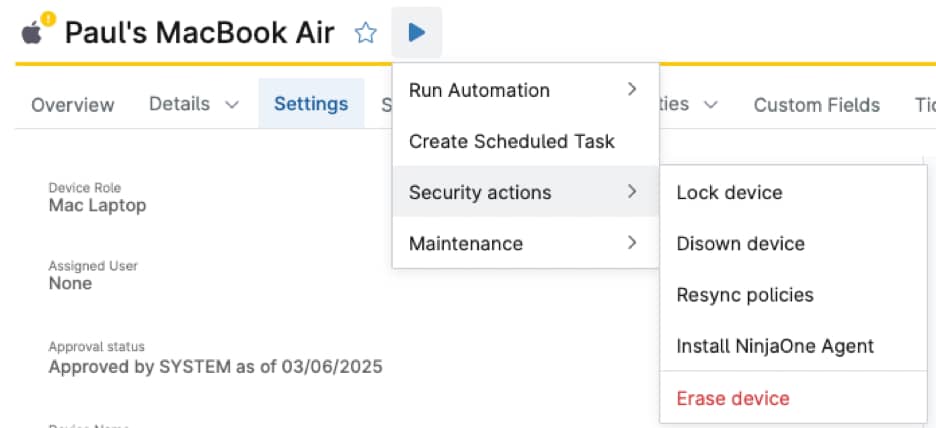
Additional macOS device actions
Finally, a new set of device actions are available to technicians with MDM-enrolled Macs:
- Lock device – This reboots the device into a special recovery partition. The technician specifies a PIN, and only that PIN can be used to unlock the device.
- Disown device – Releases the device from Apple Business Manager or Apple School Manager.
- Resync policies – Reapplies all configurations in the assigned policy.
- Install NinjaOne agent – Deploys, or redeploys, the NinjaOne RMM agent to the device.
- Erase device – Remotely wipes the device. Equivalent to selecting “Erase all Contents and Settings” from the device in System Settings.
Additionally, deleting the device record from NinjaOne will automatically remove the installed enrollment profile, as well as any other configuration profiles.
What’s next?
NinjaOne is able to combine these MDM-based capabilities with our existing agent-based capabilities and offer the full management of macOS devices. NinjaOne now has the framework in place to continue expanding supported capabilities across Apple’s MDM and DDM protocols for macOS, iOS, and iPadOS.
At the same time, our product roadmap is largely driven directly by feedback from our customers and users. As we continue to build and expand our support for Apple devices, let our teams know exactly what capabilities you need to provide a best-in-class management experience for your technicians and end users. Finally, stay tuned throughout this year and beyond as we continue to build new features, support new enrollment methods, and offer support to more types of Apple devices!