To celebrate Halloween and the last day of Cybersecurity Awareness Month, we’re shedding light on the five types of phishing attacks, including spear phishing, along with two of the most popular phishing lures that criminals are using to sneak their way past defenses and into inboxes. Share these phishing email examples with your clients as a reminder to stay vigilant while you’re hard at work protecting them from day in and day out.
What is a phishing email?
A phishing email is a fraudulent email that’s sent with malicious intent, such as illegally obtaining a person’s or an organization’s security codes, data, or resources. Essentially, the purpose of a phishing email is to trick someone into revealing information or performing an action by impersonating a figure of authority or a legitimate organization. There are a few different types of phishing, such as pharming and vishing, but we are going to focus on email phishing in this post.
How to identify a phishing email
Fortunately, many email phishing scams can be avoided if employees are trained to identify them. There are a few signs you can look for to identify a phishing email:
-
Be wary if the email is poorly written
While people and organizations sometimes make minor errors in their emails, it’s highly unlikely for them to send messages with major grammatical errors and poorly-written content. Keep an eye out for glaring grammatical errors, spelling mistakes, and strangely-worded sentences. And always remember, if something seems off, it usually is!
-
Hover over suspicious links or URLs
Usually, phishing emails will strongly encourage readers to click on a malicious link. Before you click on a link, always hover over it to examine the URL and determine if it’s legitimate. Another way to check if a suspicious link is legitimate is to right-click on the link, copy it, and paste it into a word processor. Then, you will be able to check the link for errors, such as spelling and grammar errors, to determine if it is safe.
-
Check the logo
If a phishing email is attempting to impersonate an organization, it will usually include the organization’s logo. Check the logo before following any of the email’s instructions, and use caution if the logo is low-resolution or altered in any way.
Phishing email examples and how to prevent them
Phishing email: Office docs encouraging you to enable macros
What is the Office and macros phishing email?
A classic. The witch or dracula of malspam disguises. Attackers send would-be victims emails with an Office file attachment (typically Word, but sometimes Excel or even Publisher files) or a link to the file. These files are often made to look like invoices or other business-related documents to create a sense of urgency. Inside, attackers have hidden malicious macros that, when enabled, launch a chain reaction of commands that typically results in malware being downloaded from the Internet and executed.
This technique has been around for years, and it continues to see heavy usage from some of today’s most active malware operations, including Emotet — by some measurements, currently the most prevalent malware threat.
48% of malicious email attachments are Office files.
Why is it still so common after all these years? The answer is simple: It just works.
What makes the Office and macros phishing email effective?
For one thing, Office documents are such a familiar and ubiquitous part of day-to-day work. In most cases, it’s not practical to filter them, and employees rarely think twice about receiving them. Many antivirus and email security tools can also have a difficult time analyzing these files for a suspicious macro virus, especially if the file is placed inside a zip file or password protected.
What’s more, attackers are increasingly raising their game to make the context in which these files are delivered more believable. Take, for example, the Emotet gang’s nasty trick of stealing email content from its victims and using it to send incredibly deceptive emails to the victim’s contacts.
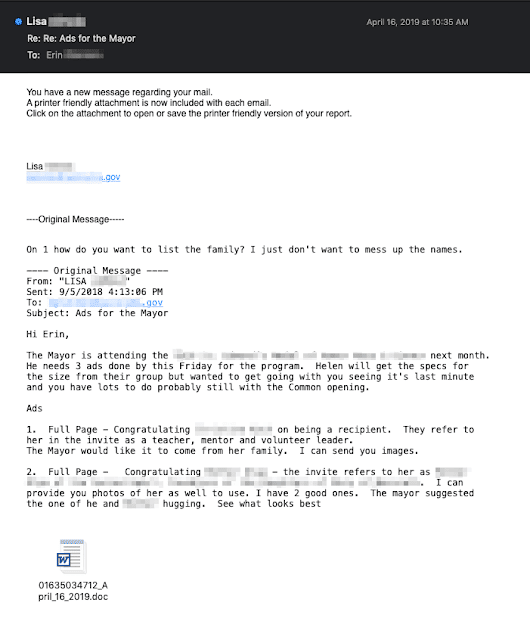
Researchers at Talos describe the tactic by breaking down this real example email below:
The email above illustrates Emotet’s social engineering. In this example, we have a malicious email from Emotet, and contained inside the body of the email, we can see a previous conversation between two aides to the mayor of a U.S. city.
- Initially, Lisa sent an email to Erin about placing advertisements to promote an upcoming ceremony where the mayor would be in attendance.
- Erin replied to Lisa, inquiring about some of the specifics of the request.
- Lisa became infected with Emotet. Emotet then stole the contents of Lisa’s email inbox, including this message from Erin.
- Emotet composed an attack message in reply to Erin, posing as Lisa. An infected Word document is attached at the bottom.
It’s easy to see how someone expecting an email as part of an ongoing conversation could fall for something like this, and it is part of the reason that Emotet has been so effective at spreading itself via email. By taking over existing email conversations and including real Subject headers and email contents, the messages become that much more randomized and more difficult for anti-spam systems to filter.
How to prevent the Office and macros phishing attack
Because these files can be disguised as anything from invoices to shipping notifications — and because they can even appear to be sent from people the recipients know and trust — the best way to protect yourself is to encourage employees to be suspicious anytime an Office doc encourages them to enable macros.
In many cases, that’s a tell-tale sign that something may not be right.
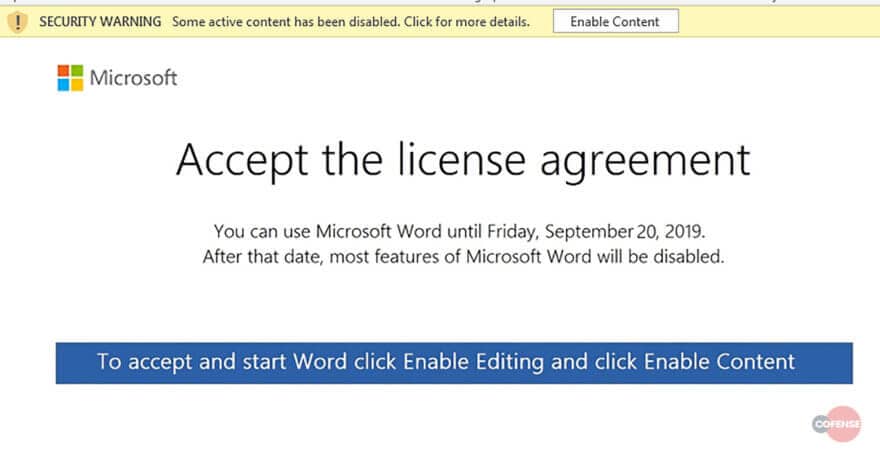
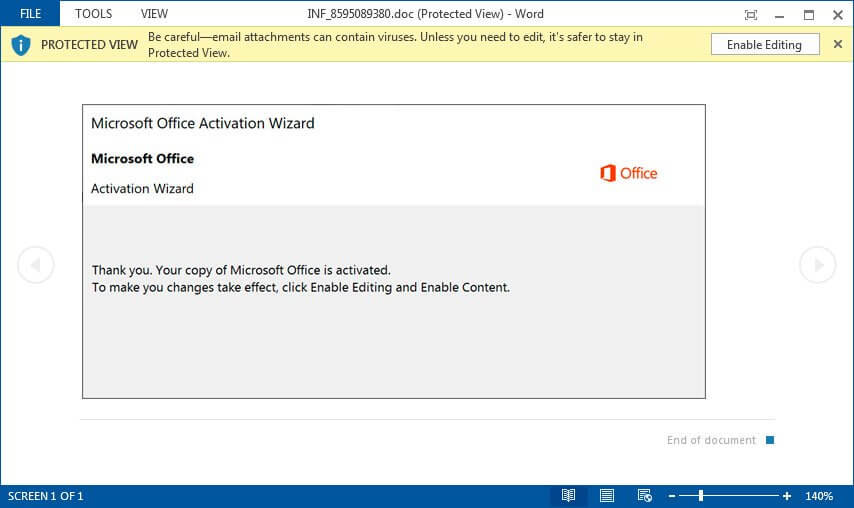
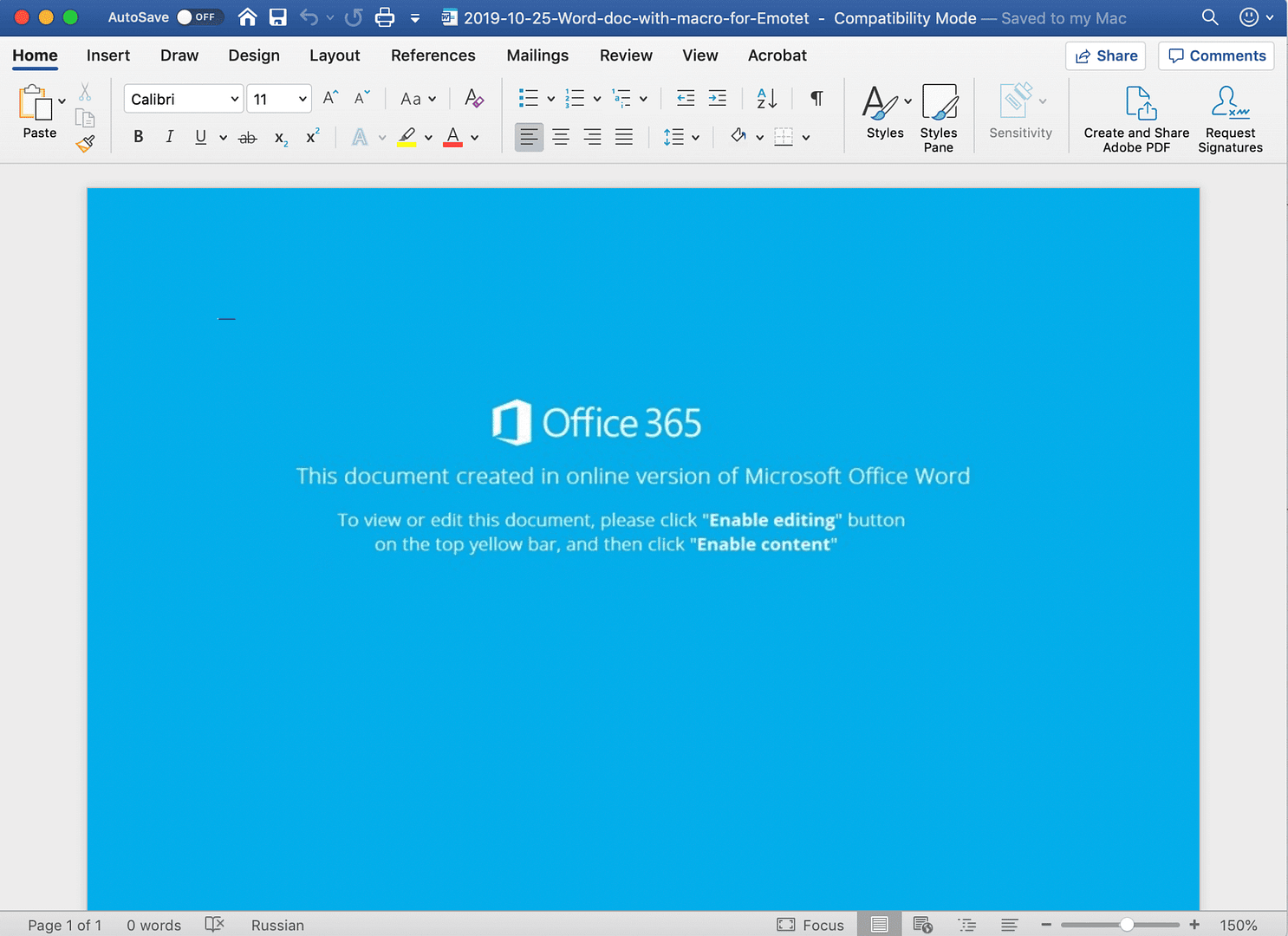
Emotet threat actors utilize a variety of lures to convince victims enabling macros is necessary, from messages indicating the document was created in a different version of Word to Microsoft licensing or Activation Wizard prompts.
Source: Cofense
Source: Bleeping Computer
If your client operates in an environment where macros are required and common, then encouraging heightened suspicion may not be practical, but if that’s not the case, then you can also consider going a step further and blocking macros from running in Office files from the Internet.
Phishing email: Microsoft 365 alerts
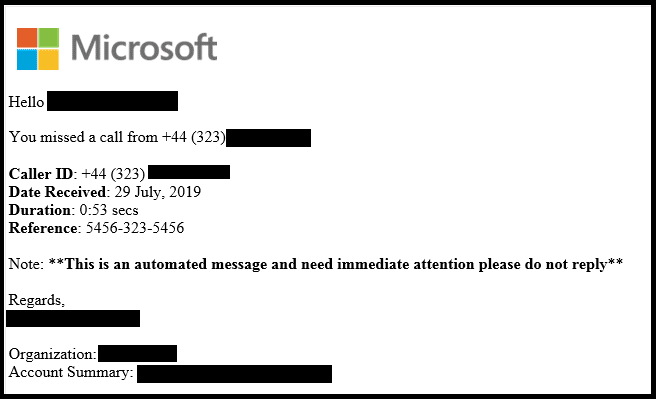
What is the Microsoft 365 alert phishing email?
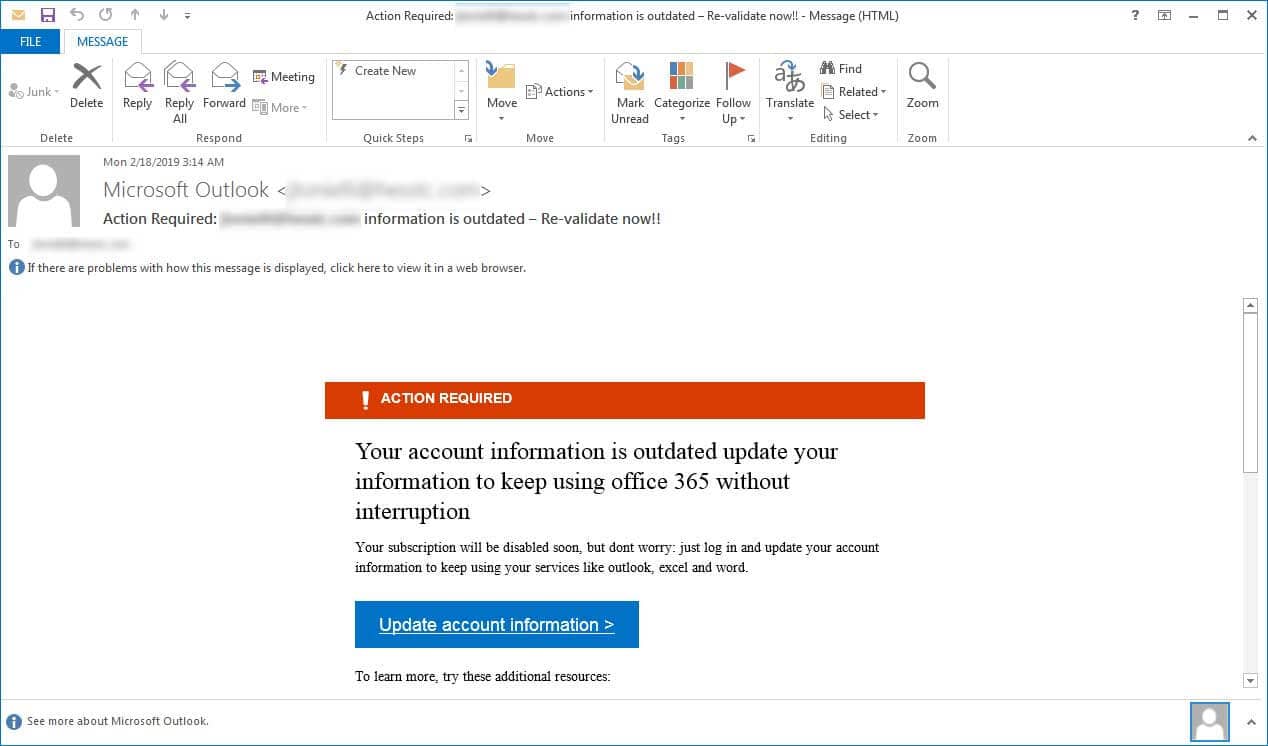
Attackers love going after Office 365 credentials. They open the door to a world of malicious opportunities, including additional spear phishing and — thanks to how common it is for passwords to be reused — additional access and lateral movement attempts.
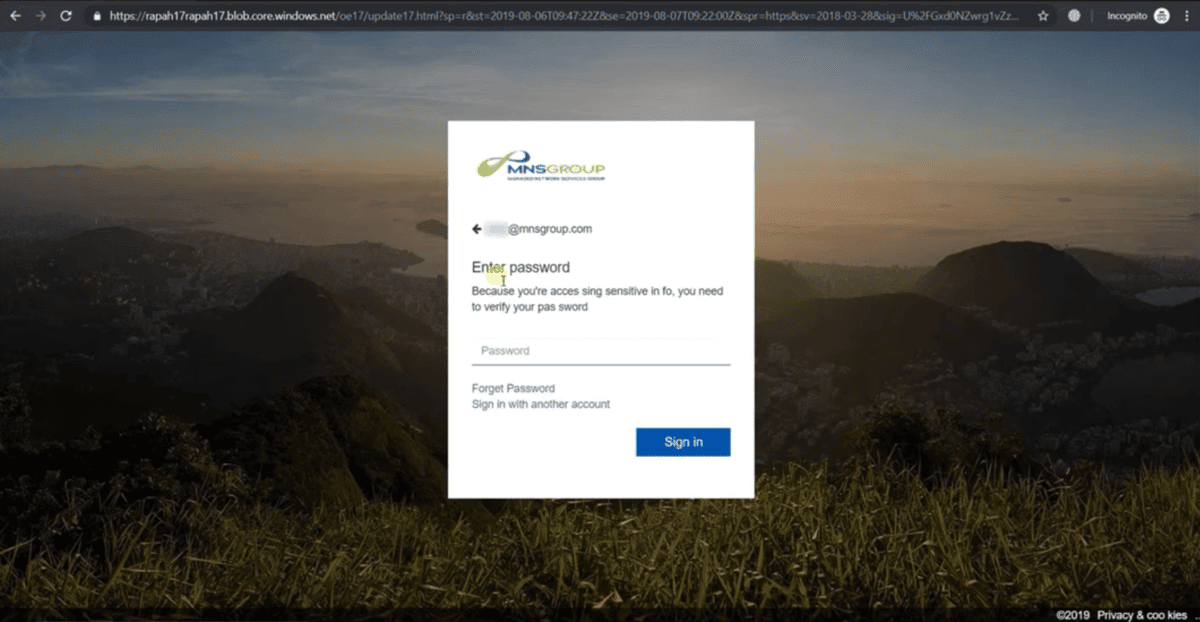
Emails often take the form of fake notices from Microsoft, alerting users that they have undelivered messages or that action is required to continue using their account. Clicking the links provided in these emails typically takes the recipient to a realistic-looking Microsoft sign-in page, where the user is asked to provide their credentials.
Source: Bleeping Computer
Campaigns have also included fake voicemails that are actually HTML attachments. When opened, these files play a brief audio recording then also redirect the recipient to a fake Microsoft landing page, prompting them to enter their password to hear the full voicemail.
Source: McAfee
What makes the Microsoft 365 alert phishing email effective?
Users are much more likely to trust an email that looks like it was sent from Microsoft than an unknown entity. It’s one of the reasons why Microsoft is the most commonly impersonated company in phishing emails.
Microsoft is #1 impersonated brand by phishers, with an average of 222 unique Microsoft phishing URLs popping up every day.
Attackers have adopted the tactic of hosting their fake Microsoft sign-in pages on Azure Blob Storage URLs, which use the windows.net domain and a valid certificate from Microsoft. That adds legitimacy to these pages and makes it easier for them to slip past filters.
As this video from a webinar we did with Huntress Labs CEO Kyle Hanslovan shows, attackers can even customize these pages to include the name and company logo of targeted victims, adding even more legitimacy.
How to prevent the Microsoft 365 alert phishing attack
Spotting these attempts requires being alert and looking for all the standard phishing giveaways — checking the sender name and address, hovering over links to see the URL before clicking, etc. Ex: One of the landing pages Kyle highlights in the video above is “misocroft” — close enough to Microsoft to pass at a quick glance.
In addition to training users to spot the tell-tale signs of phishing emails, you can also consider creating a rule to alert you or users if an email contains the windows.net domain.
Protect Your MSP Business and Keep Your Clients Secure with this Cybersecurity Checklist
Are you checking all the boxes when it comes to securing your MSP? Find out with our comprehensive checklist. Download it here.