Cybersecurity isn’t just at the top of the discussion queue within the IT channel. Businesses and governments worldwide have turned a sharp eye toward rising cyber threats and SMB cybersecurity statistics.
Many have learned the hard way that small businesses are frequent targets of all types of cyberattacks. The idea of “targeting a victim” itself has come into question, and more realize that widespread, indiscriminate attacks are the status quo. As a result, SMEs are more vulnerable to such approaches as they typically lack the awareness, internal IT staff, and cyber posture to resist them.
This is only one of many realizations that have emerged in the cybersecurity sector over the last year. Many new trends are on the rise — as are new threats — and MSPs are finding themselves in a position where they must adapt or face significant damage to their businesses. We’ve curated several other significant cybersecurity trends for 2024 in the following article.
What this article will cover:
- How many businesses are still vulnerable to cyberattacks?
- What are the leading cyber threats in 2024?
- Antivirus takes a backseat to endpoint protection
- The state of ransomware in 2024
- What MSPs can do about SME cybersecurity
1. The vast majority of businesses are still vulnerable to attack
Hackers can penetrate at least 93 percent of company networks.
According to recent research, betanews tells us that cybercriminals can reliably penetrate 93 percent of organizations’ networks. Additionally, the emergence of AI has made these attacks less detectable.
Positive Technologies conducted a series of pen tests across several large sectors, including finance, fuel and energy, government bodies, industrial businesses, and even IT companies. They proved that in 93 percent of test cases, an attacker could breach an organization’s network defenses and gain access to the local network.
A study by CISCO reveals that 40% of the SMEs that faced a cyberattack experienced at least eight hours of downtime. Downtime accounts for much of the overall financial damages of a security breach. (Source)
On top of that, more attacks are being targeted at small and medium-sized businesses. While 43% of cyber attacks are aimed at small businesses, only 14% are considered prepared, aware, and capable of defending their networks and data. (Accenture’s Cost of Cybercrime Study)
Additionally, as pointed out in Cybersecurity Magazine (Source):
- 30% of small businesses view phishing as their biggest cyber threat
- 83% of small and medium-sized businesses are not prepared to recover from the financial damages of a cyber attack
- 91% of small businesses haven’t purchased cyber liability insurance, despite awareness of risk and the likelihood that they would be unable to recover from an attack
- Only 14% of small businesses consider their cybersecurity posture as highly effective
Why are businesses still hesitant to embrace a more robust approach to security? While cybersecurity statistics are good for understanding the nature of the threat environment, they don’t always work well as a tool for changing perceptions. Toward that end, many in the cybersecurity and channel community have advocated for a change in attitude toward cybersecurity adoption.
2. The leading cyberthreats in 2024
Humans are still being exploited as the “weakest link” in a cybersecurity plan.
Email phishing, spear-phishing, and social engineering continue to trend as the most common and reliable means of illegally accessing a network. Over 12 million phishing and social engineering emails landed in the mailboxes of more than 17,000 U.S. organizations in 2021 alone. In addition, 85% of breaches involved a human insider, and 61% of breaches involved weak passwords or compromised credentials.
Social engineering and phishing are the most frequently used methods. Even when the appropriate software, hardware, and patches are in place, the human element still provides a weak point for entry. As we all know, this attack vector only became more viable after the pandemic, as many businesses turned to remote workplace modalities and rushed themselves through the digital transformation process as a matter of survival. Numerous studies have shown that cyber risk increased in line with increases in remote work.
In addition, these reports revealed:
- 70% of office workers use work devices for personal tasks (Source)
- 37% of office workers use their personal computers to access work applications (Source)
- 57% of data breaches could have been prevented by installing an available patch (Source)
3. Credentials and admin access management
Vastly more breaches have been linked to account compromises and poor permissions control than viruses.
One common thread in the modern cybersecurity narrative is a general shift away from the importance of AV and firewalls and an increased focus on endpoint security. Despite this, one out of five small businesses don’t have any endpoint protection in place. This could be due to the fact that over half of small businesses in the U.S. lack any in-house IT support, much less cybersecurity expertise.
This means that the onus of SME endpoint security falls upon Managed Service Providers (MSPs) in most cases. MSPs must make small businesses aware of the need for password hygiene, permissions control, and other endpoint security measures like data encryption. At the very least, MSPs should be actively embracing the principle of least privilege when it comes to admin account management in their clients’ networks.
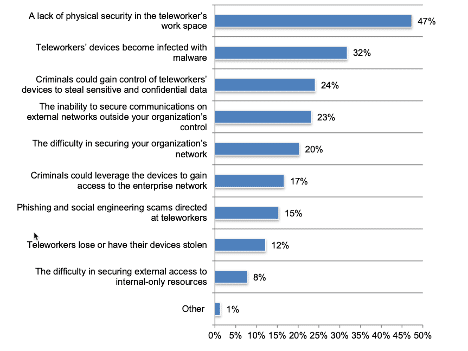
Around 58% of organizations around the world use “telework” workforces, and that number is steadily climbing. Businesses are aware that remote working creates a number of security challenges, and this Ponemon survey reveals how they prioritize their concerns:
4. Ransomware is still a threat
The simplicity and efficacy of ransomware continue to make it a preferred choice for hackers.
- Malware increased by 358% and ransomware increased by 435% in 2020. (Source)
- Worldwide ransomware damages and ransom payments added up to over $20 billion in 2021. This number is expected to rise to over $265 billion by 2031. (Source)
- Research on known ransomware victims shows that while 32% pay the ransom, they only get an average of 65% of their data back. (Source)
- Only 57% of ransomware attacks have been successfully mitigated by restoring backups. (Source)
- The percentage of organizations victimized by ransomware attacks continues to grow yearly, reaching 71% of organizations in 2022. (Source)
- If 2023 keeps pace for ransomware payments, it’s projected to hit $898.6 million. This would make 2023 the second-biggest year for ransomware revenue, behind 2021, which estimates $939.9 million from ransomware victims. (Source)
Learn how H.E.R.O.S. was able to quickly bounce back from a ransomware attack with minimal downtime and lasting damage.
5. There were 26448 CVEs issued in 2022
The number of critical vulnerabilities reached 4135 in 2022, up 59% from the previous year. (Source)
Vulnerabilities are expected to increase with the pace and scale of tech adoption. Cyber attacks are considered an inherent risk these days. However, this trend is creating a growing pile of security debt that MSPs and security professionals struggle to address. When cybersecurity teams leave last year’s vulnerabilities unaddressed, this year’s number becomes cumulative and significantly harder to remediate.
A report by Redscan Labs shows:
- 90% of all CVEs uncovered in 2021 were exploitable by attackers with minimal technical skills
- 55% of 2021 CVEs required no privileges to exploit
- 61% of the total CVEs in 2021 required no user interaction (such as links, downloads, installs, or compromised credentials)
- 54% of 2021 vulnerabilities were “high” availability, meaning they were easy to access and readily exploitable by attackers
6. Cloud attacks are on the rise
Organizations of any size could experience an attack targeting their cloud data.
Trends toward the cloud have of course led to a trend in cloud-targeted cyberattacks. Since 2020, 79% of companies with data in the cloud have experienced at least one cloud breach. This is no small number, as reports show 92% of organizations are currently hosting at least some of their data or IT environment in the cloud.
This is — yet again — an issue that can be traced back to the COVID-19 pandemic. The unanticipated speed at which many organizations have adopted cloud technology has created many unique vulnerabilities.
Various studies on this growing threat have shown:
- 46% of organizations use cloud-based applications purpose-built for the cloud; 54% moved applications from an on-premises environment (Source)
- 47% of companies surveyed found that users had unnecessary privileged access, and 25% experienced problems with unauthorized users (Source)
- Top cloud security concerns include data loss and data leaks (69%), data privacy (66%), and accidental exposure of credentials (44%)
- The highest ranked cloud threats are misconfiguration (human error), unauthorized access, poorly secured interfaces, and account hijacking
- End-user spending on public cloud services is expected to grow to $362.3 billion worldwide in 2022 (Source)
7. Digital supply chain attacks are considered a top risk
More threats are expected as vulnerabilities such as Log4j proliferate through the supply chain.
Even as organizational attack surfaces keep expanding, third-party risks become more critical. Gartner predicts that by 2025, 45% of organizations worldwide will have experienced attacks on their software supply chains. This represents a 300% increase from 2021.
Due to recent high-profile threats, MSPs are all too familiar with supply chain attacks. Pressure on the digital supply chain demands more risk-based vendor/partner separation, tighter security controls, best practices, and a shift toward more security-minded development and distribution. That said, it’s widely regarded that IT providers and their vendors may struggle to get ahead of forthcoming regulations brought about by this increase in risk.
Get more actionable tips with NinjaOne’s free guide on IT Security fundamentals.
Don’t go cheap on risk mitigation.
These statistics may seem daunting, and many small businesses feel helpless in the face of these numbers. After all, sophisticated cybersecurity tools and qualified experts don’t come cheap and can be hard to justify, even when an SMB knows that a cyber attack could put their company out of business. So, where does this disparity between MSPs the danger and risk mitigation cost?
Fortunately, it puts MSSPs and MSPs in a good position with businesses that realize they need security offerings but cannot afford in-house security professionals. Instead, it falls upon the IT provider to convince end-user clients of the importance of a strong security posture.
NinjaOne – The RMM That Helps Your Clients Stay Secure
- Control and Visibility
- Role Base Access
- Drive Encryption
- Managed AV
- Password Management
- Device Approval
Lean more about leveraging NinjaOne’s built-in tools to improve endpoint security.