Key Points
- Establish a structured vulnerability management process to identify, assess, remediate, and verify vulnerabilities efficiently.
- Follow CISA-recommended remediation timelines — fix critical vulnerabilities within 15 days and high-severity ones within 30 days to minimize exposure.
- Prioritize vulnerabilities by severity, exploitability, and business impact to focus resources on the most critical threats first.
- Maintain an accurate, centralized IT asset inventory for full visibility, faster identification, and quicker remediation of vulnerable systems.
- Create and enforce a vulnerability management policy with clear roles, timelines, and reporting to ensure consistent and timely remediation.
Edgescan reports that the “Mean Time to Remediation (MTTR) for Critical Severity vulnerabilities is 65 days.” They further state that one-third of all vulnerabilities were rated as High or Critical Severity in 2022. With so many risky vulnerabilities taking over 2 months to remediate, it can leave IT environments unprotected and open to attack.
To avoid the headache of a security breach, organizations must be proactive in their approach to effectively secure the IT environment. It’s crucial for MSPs and IT professionals to implement vulnerability remediation timelines best practices to ensure that vulnerabilities are remediated and that their IT assets and associated data are protected promptly. These best practices also help businesses to set practical time frames for handling and addressing these vulnerabilities.
To see how these best practices unfold, you may watch this short video: ‘Vulnerability Remediation Timelines: 7 Best Practices’.
Accelerate vulnerability remediation timelines with NinjaOne.
7 vulnerability remediation timelines best practices
1. Establish a vulnerability management process
A vulnerability management process is a set of procedures that guides how vulnerabilities are identified, evaluated, and remediated. This process is essential for your business to know how to properly address certain vulnerabilities in your IT environment.
How to do it:
The four key steps of a vulnerability management process are to locate and identify vulnerabilities, evaluate them, monitor and remediate the identified vulnerabilities, and finally confirm whether the vulnerabilities have been mitigated. With the help of RMM software, IT pros can simply monitor the environment for vulnerabilities and remediate any issues using the software.
Why it’s important:
Establishing this process will guide your company’s actions in addressing weak spots in your IT systems that are vulnerable to exploitation. This process is also foundational to the creating vulnerability remediation timelines, as it contains all the necessary steps to account for in your timelines.
2. Follow remediation guidelines
When establishing a plan for addressing vulnerabilities, it is wise to consult organizations and agencies that are in the know. For example, the Cybersecurity and Infrastructure Security Agency (CISA) states that high vulnerabilities should be remediated within 30 days and critical vulnerabilities should be remediated within 15 days of detection. Then, when your IT team creates a plan for vulnerability remediations, these guidelines can be incorporated.
How to do it:
Rather than attempting to establish your own timelines for resolving vulnerabilities, consult organizations like CISA. Create a step-by-step plan that enables your organization to remediate vulnerabilities within the recommended time frame.
Why it’s important:
IT vulnerabilities all carry a risk of exploitation. However, some may have a greater impact on the organization than others. Any high or critical-level vulnerabilities should be quickly addressed, but all IT vulnerabilities must be remediated within the recommended time frames.
Learn more in our NinjaOne Patch Management FAQ to see how automated patching helps you meet remediation timelines.
3. Prioritize vulnerabilities
Prioritizing IT vulnerabilities based on their severity and exploitability is essential. Doing so allows you to dedicate and allocate the necessary resources for remediation, and plan your remediation timelines accordingly. Ranking vulnerabilities also allows you to establish the potential impact the vulnerabilities will have on the organization and helps you to determine where certain remediations need to fit into your remediation timelines.
How to do it:
Establish a system for ranking potential IT vulnerabilities. Base it on potential business impact, severity, and the likelihood of exploitability. Once your organization’s ranking system is established, prioritize and address the most severe vulnerabilities first on the timeline.
Supplement CVSS scores with EPSS (Exploit Prediction Scoring System) to prioritize remediation. EPSS predicts the active exploit likelihood within 30 days, focusing resources on the most immediate threats.
Why it’s important:
Prioritizing the most critical vulnerabilities helps businesses to strategically address and remediate them. Ranking vulnerabilities also allows businesses to create a plan and remediation timeline to address vulnerabilities in order of severity.
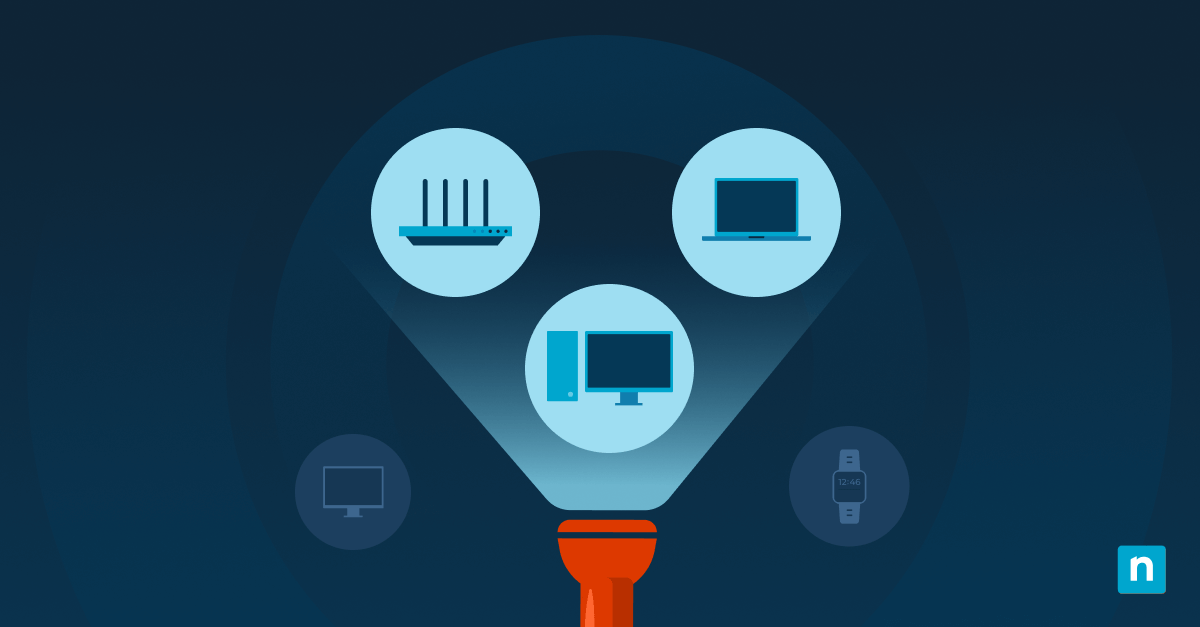
4. Keep track of your IT assets
Keep an updated inventory of all your hardware and software assets. Ideally, this information should all be kept in one central location. By tracking all your organizational assets, you can to identify vulnerable assets, prioritize them based on your ranking system, and remediate them accordingly.
How to do it:
Use tools to track your IT assets that give you increased visibility into your IT environment, like NinjaOne’s IT asset management software. Regularly scan the environment for new devices or applications to ensure your IT asset inventory is continually updated.
Why it’s important:
An up-to-date IT asset inventory provides you with correct information about your IT environment so you can accurately identify vulnerabilities within the entire infrastructure. With full visibility into the environment, it helps prevent assets from being overlooked and enables quicker identification of vulnerabilities. This helps to speed up the remediation so your systems are vulnerable for a shorter amount of time.
Check out our IT Asset Management FAQ to learn how asset visibility supports faster vulnerability remediation.
5. Create a vulnerability management policy
Vulnerability management policies outline how your organization handles the management of vulnerabilities within its IT environment. This type of policy states the plans and agreement for how and when vulnerabilities will be addressed and remediated. A patch management policy is an example of a vulnerability management policy, which contains documentation on how patches are managed and applied to endpoints within an organization.
How to do it:
Create a policy with clear guidelines on how to handle the identification, assessment, and remediation of vulnerabilities. Assign specific vulnerability management roles to employees or specified end users to ensure the policy is implemented.
Why it’s important:
A vulnerability management policy keeps your IT team accountable for how vulnerabilities are handled. If remediation deadlines are missed, the policy must mandate formal Risk Acceptance by a senior leader. This acceptance requires the immediate use of a compensating control (such as network segmentation or temporary patching) to mitigate the threat. It helps to ensure that any potential risks in your IT environment are effectively addressed in a timely manner. Policies also provide structure to risk management, which help your organization to meet your remediation timeline goals.
6. Vulnerability remediation reporting
Generating a report on the progress and outcomes of your vulnerability remediation efforts. This will allow you to determine what’s working, areas that may be lacking, and decide where to focus future efforts.
How to do it:
Regularly generate vulnerability remediation reports on the number and type of vulnerabilities identified, and how well they were addressed. Important metrics to track include: Mean Time to Detect (MTTD), Mean Time to Remediate (MTTR), and the Remediation Compliance Rate (the percentage of critical/high vulnerabilities remediated within the established policy window). Include information about how quickly remediations took place, and whether they met the time frame goals.
Why it’s important:
In order to know whether you’re meeting your vulnerability remediation timeline goals, reporting is essential. It helps you know how well your remediation efforts are working and determine if changes need to be made.
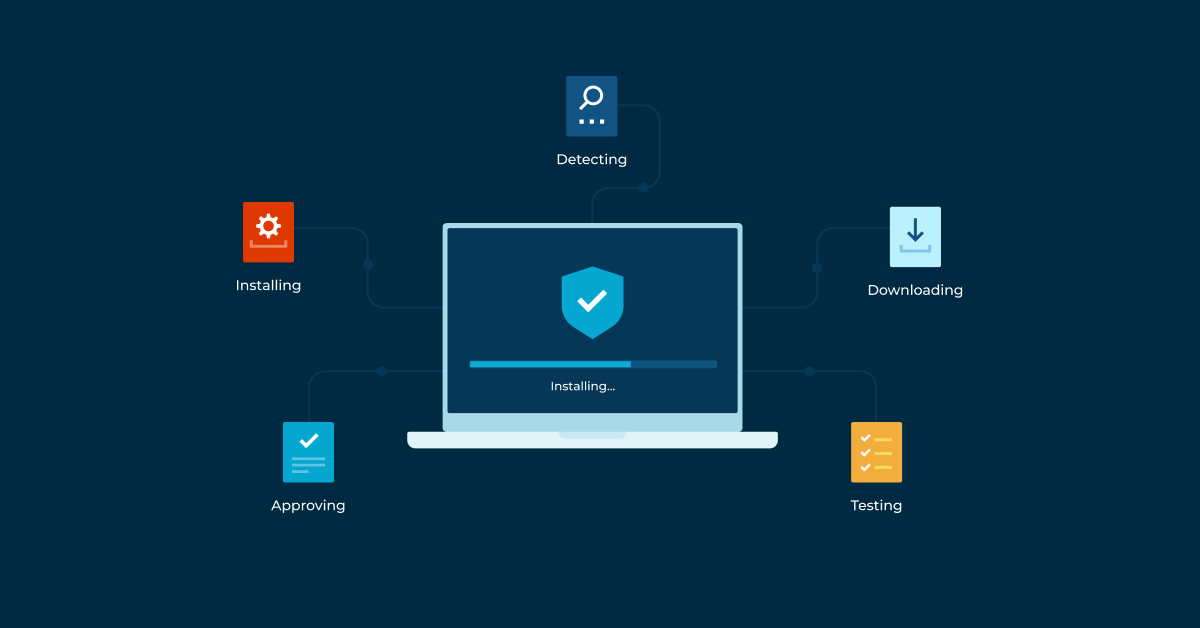
7. Implement IT automation
IT automation tools can speed up vulnerability management processes and streamline repetitive management tasks. It eliminates human error, allowing devices and your IT environment to be quickly protected and secured.
How to do it:
Use software to automate specific tasks within your vulnerability management process, such as patch deployment and vulnerability scanning.
Why it’s important:
Manual remediation of IT vulnerabilities can be a time-consuming process and may prevent you from reaching your remediation timeline goals. IT automation frees up your technicians to perform other tasks and ensures that essential vulnerability management and remediation tasks are completed in a timely manner.
Detect, prioritize, and remediate vulnerabilities faster with NinjaOne.
→ Get started with a free trial or watch a demo.
Automated vulnerability remediation
NinjaOne’s software helps organizations get full visibility into their environment and reduce IT vulnerabilities. Our automated vulnerability management software allows organizations to rest assured that their IT environment is being actively protected at all hours of the day.
Watch a demo or sign up for a free trial of NinjaOne’s vulnerability management software to see how Ninja can improve your endpoint security.