What is Application Management on Mobile Devices?
Application management on mobile devices is typically handled through Mobile Application Management (MAM). MAM is a set of tools and practices that allows IT administrators to securely control and manage applications on smartphones, tablets, and other mobile devices. Here is a breakdown of what MAM offers:
- Secure App Distribution and Updates: IT admins can distribute company apps or approved third-party apps to devices. They can also manage updates for these apps, ensuring everyone has the latest secure version.
- Containerization (Android only): MAM can create secure containers on a device to isolate business data from personal data. This ensures that even if the device is lost or stolen, sensitive work information remains protected.
- Access Control: MAM allows IT to control which apps users can access and what data they can share with those apps. This helps prevent unauthorized access to sensitive information.
- Remote Wipe: If a device is lost or stolen, IT can remotely wipe the corporate data from the device using MAM. This protects sensitive information from falling into the wrong hands.
- Improved Productivity: MAM can help ensure employees have the necessary applications for their jobs and keep those applications up to date. This can improve overall productivity.
How Can MAM be Implemented in an Organization?
implementing Mobile Application Management (MAM) in an organization involves selecting the right MAM solution, developing robust policies, configuring the system, enrolling devices, enforcing security measures, and providing continuous support and training. Regular review and improvement are essential to adapt to evolving needs and maintain a secure and efficient mobile application environment.
How to Configure Mobile Application Management in NinjaOne?
Mobile Application management can be implemented in NinjaOne through policies. There are policies designed for mobile devices called MDM policies, which can be applied to Android, iPhone, or iPad devices. MDM policies have an Applications section, where you can add the applications for the devices linked to this policy.
NinjaOne also offers a Kiosk mode, which only allows one single application to run. This is useful for mobile devices that need to perform specific tasks or that are accessible in self-service mode, such as interactive kiosks, mobile points of sale, etc.
Strategy: Install Approved Applications on The Work Profile for a BYOD Android Phone
BYOD stands for Bring Your Own Device, and it refers to an employee-owned device which is also used for work. In such a case, when the device is enrolled for work applications, a separate profile will be created on the device. Applications and data stored on the work profile cannot interact with the personal profile, making the work profile secure.
In this example, we will create an MDM policy called Android BYOD, and we will add some applications that will be automatically installed on the work profile.
A) Follow the next directions to create the MDM policy:
1. Go to Administration, then Policies, and then MDM Policies.
2. Click Create New Policy.
3. In Name type Android BYOD.
4. In description, type the description of your choice, for example, MDM Test Policy.
5. In Role, select Android.
6. In Parent Policy, select Android Mobile Policy.
7. Click Save
(see the next screenshot for reference)
8. The Policy editor appears.
B) Once the Policy has been created, follow the next directions to add approved applications:
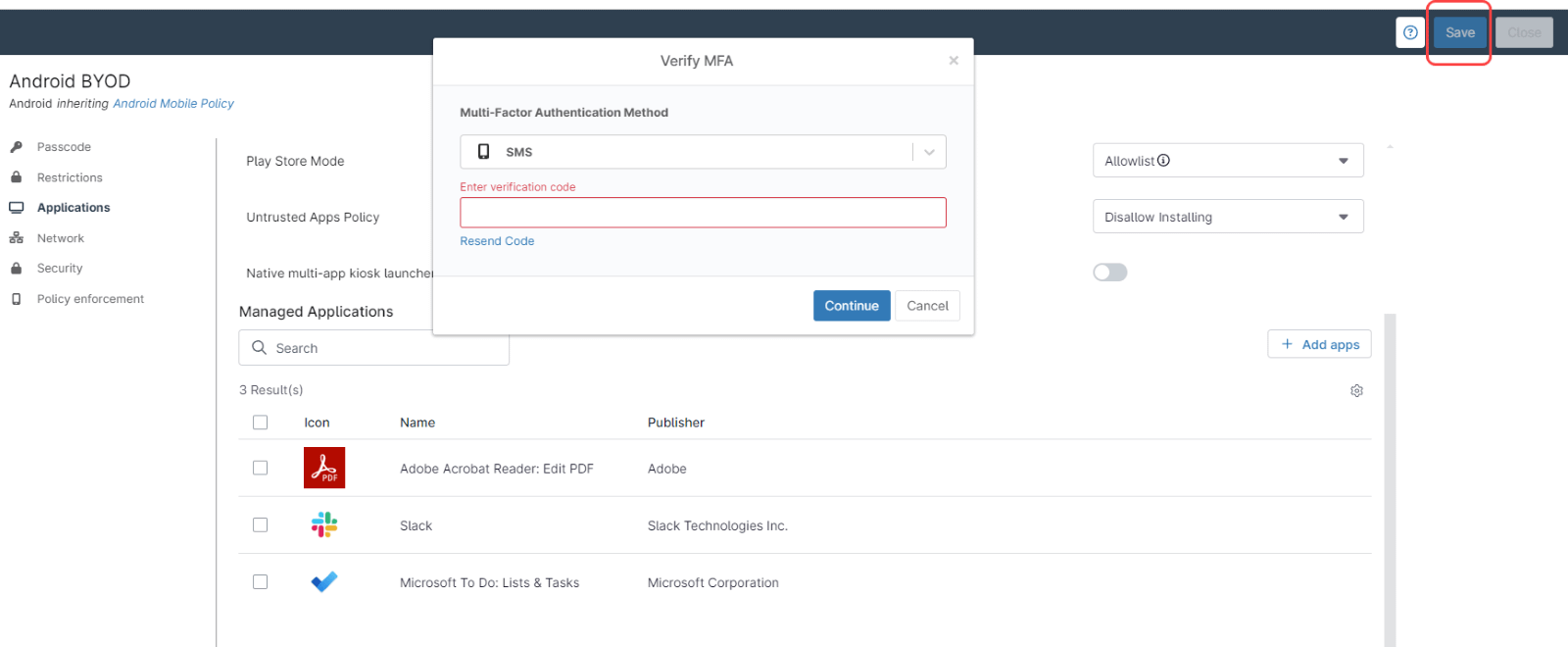
1. On the left side, select the Applications tab.
2. Under Default Permission Policy, select Grant.
3. In Play Store Mode, select Allowlist.
4. In Untrusted Apps Policy, select Disallow Installing.
5. Keep the Native multi-app kiosk launcher option off (default).
6. Click add apps and select Play Store. The Play store screen appears.
7. Click on Adobe Acrobat Reader, then click on Select. The Play store screen disappears.
8. Check the newly added app and click the blue Edit button.
9. In Assignment type, select either Force Installed or Preinstalled. The difference is that the force installed applications cannot be uninstalled from the work profile by the end user.
10. On Default Permission Policy, select Grant.
11. On Connected Work and Personal App, select Unspecified.
12. Auto Update Mode, select Default.
13. Click Save.
14. At this point, you can continue adding applications in the same way we added Adobe Acrobat Reader, once you´re done, click Save on the upper right side of the screen. Enter your MFA method response and close.
(see the next screenshot for reference)
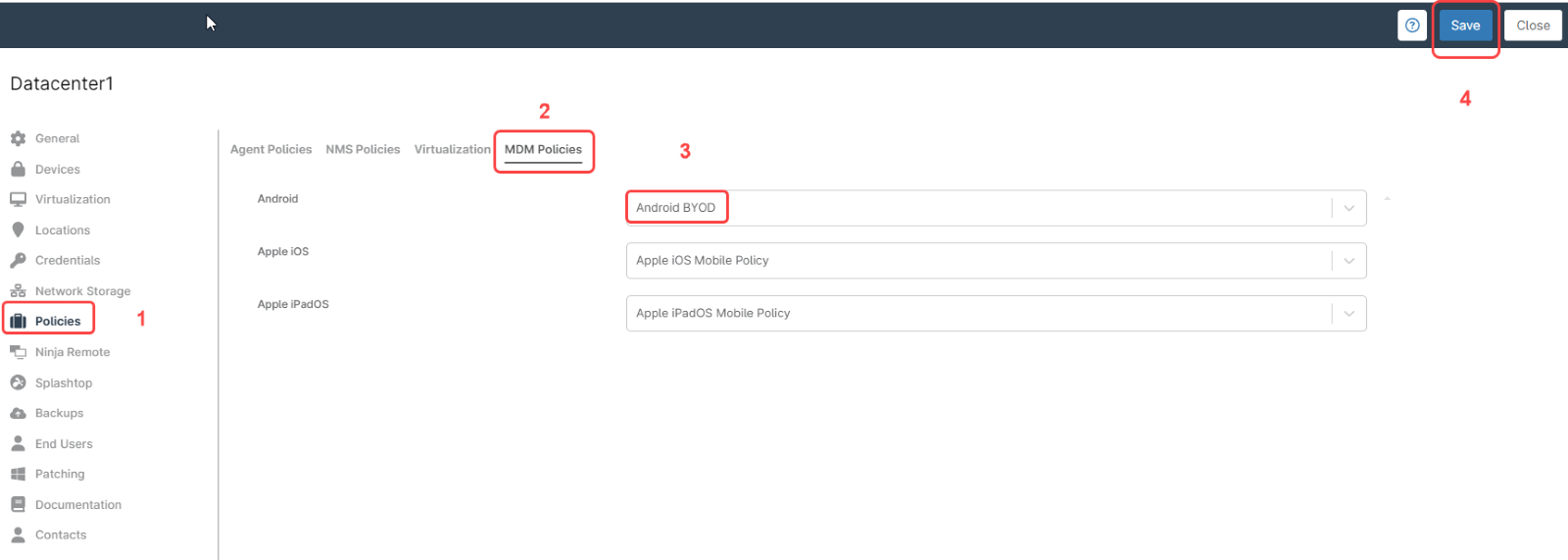
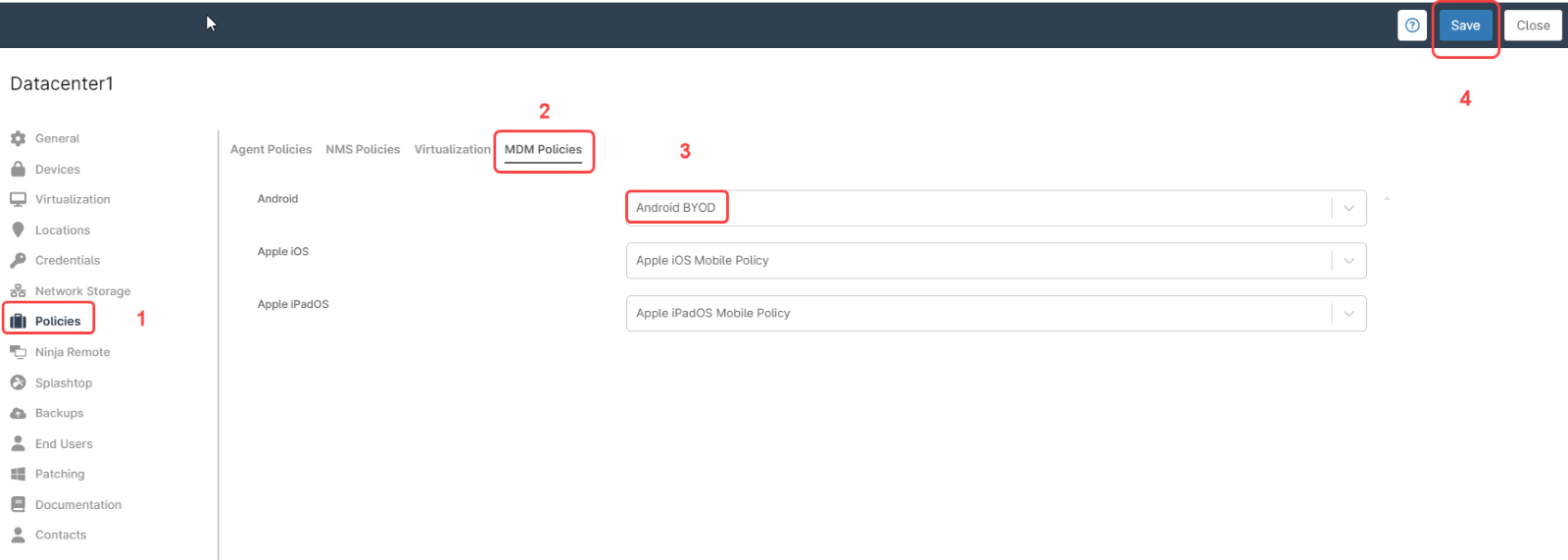
C) Set the newly created policy as the default policy for your organization, for that, go to your organization’s dashboard and click edit, then:
1. On the left side, select the Policies tab.
2. On the right side, select the MDM policies tab.
3. On Android, From the dropdown menu, select the Android BYOD policy we created in the last step.
4. Click Save.
(see the next screenshot for reference)
D) Enroll an Android device to your organization:
Prerequisite, install the Android Device Policy (ADP) on your android device. Android version must be 9 or later.
1. From any dashboard, click on the + sign on the upper right of the screen.
2. Select Device and then Mobile Device. A dialog box appears.
3. Fill out your organization name and location.
4. On Device Role select Android.
5. On usage type select For Personal and work.
6. Click on Generate QR code. A screen with a QR code and instructions will appear.
7. On your Android device, open the ADP application and scan the QR code from it.
8. Follow the instructions on the Android device.
After a few minutes, a work profile will be created on the Android device and the applications that we selected on step B will be auto installed, while the device´s settings and personal profile remain untouched.
What Are The Advantages of Using NinjaOne for Mobile Application Management?
-
Unified management
Mobile devices can be managed from the unified console, the same as all other devices.
-
Cost savings
Policies streamline application management, saving time and resources.
-
Integration with Other Tools
The platform integrates with other IT management and service desk tools, providing a more cohesive and efficient IT management ecosystem.