
Helpdesk Efficiency Guide
Learn how to turn automation and smarter organization into a killer efficiency combo.

Learn how to turn automation and smarter organization into a killer efficiency combo.

Save time with a pitch that gets to the heart of what decision makers need to see, including a readiness checklist, executive briefs, a presentation deck, and a helpful ROI calculator.

See the latest statistics on how IT is managing the new challenges and opportunities of remote and hybrid work environments.
With the tech labor market being the tightest in recent history, doing more with less is imperative for any growth-focused IT business.
Most IT helpdesks are built to handle incidents reactively, using a process that forces IT teams, to rely on a negative outcome before remediation can begin.

With the right data protection tools, you can ensure data is backed up and restorable.

How Legacy Technology Impeded Post-Pandemic Growth.

Wondering how to better manage devices for distributed workforces? Here is a guide on what MDM and RMM are, when to use them, how it works, and why you need them.

New research from NinjaOne found that 77% of businesses are spending more than 3 hours per endpoint per month on patch management. Read the full report to learn how manual processes could be costing IT teams time, money, and exposing them to new risk.

Get your how-to guide to tackling 10 of the most common IT time wasters. Learn how to reduce ticket volume 20%-50%, stop relying on end users to regularly reboot their devices, enable users to restore their own files and save time, and more.

Shadow IT, or unmanaged devices or software, in an organization represents an opportunity for MSPs to deliver more value and tighten their clients’ security. The truth is, shadow IT isn’t so innocent and it carries the risk of violating data privacy laws, distorting IT budgets and more. Read more to get insight into how shadow IT is impacting the organization and how to turn security gaps into opportunities.
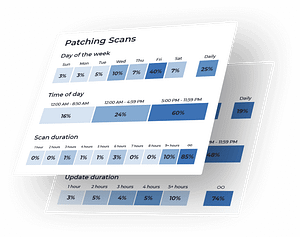
Get insight into when to schedule patching scans and updates, how to configure patching approvals, the most common patching profiles, and more.
Wondering what you should be monitoring with your RMM? This remote monitoring checklist will give you 28 recommendations to implement.

Making the Case for Remote Monitoring and Management This infographic provides you with the facts and insights you need to make the case for an

Still manually managing BitLocker disk encryption? Use NinjaOne and PowerShell to automate encryption along with collecting and storing recovery keys.

Learn how NinjaOne can help you automate the process of remotely uninstalling software across client end-users or entire organizations.

Kelvin Tegelaar, author of the popular blog CyberDrain.com, provides simplified overviews of fundamental PowerShell concepts plus straightforward walkthroughs that put those concepts into action.
Adam Bertram of GitHub is back to tell you all about how to utilize PowerShell to sync information from CSVs with Active Directory. Check out his post to learn helpful tips, tricks, and safety precautions.

Everyone knows the importance of a clean Active Directory, but it’s finding the time to clean it that becomes the issue. Here are three ways we suggest for how to keep your Active Directory clean.